11-19, 16:50–17:35 (Europe/Vienna), Urania Dachsaal
Electronic Shelf Label (ESL) tags are increasing in popularity. More and more stores switch their price tags to digital ones for various reasons, such as competing with online wholesalers.
In this talk, we analyzed the 433MHz connection of a popular ESL tag and identified multiple security flaws that allowed us to spoof the RF signal
and display arbitrary content on the displays. Furthermore, the original manufacturer of the E-Tag labeled microcontrollers was discovered.
This talk will give an overview of analyzing unknown hardware with an unknown RF protocol without any prior known research.
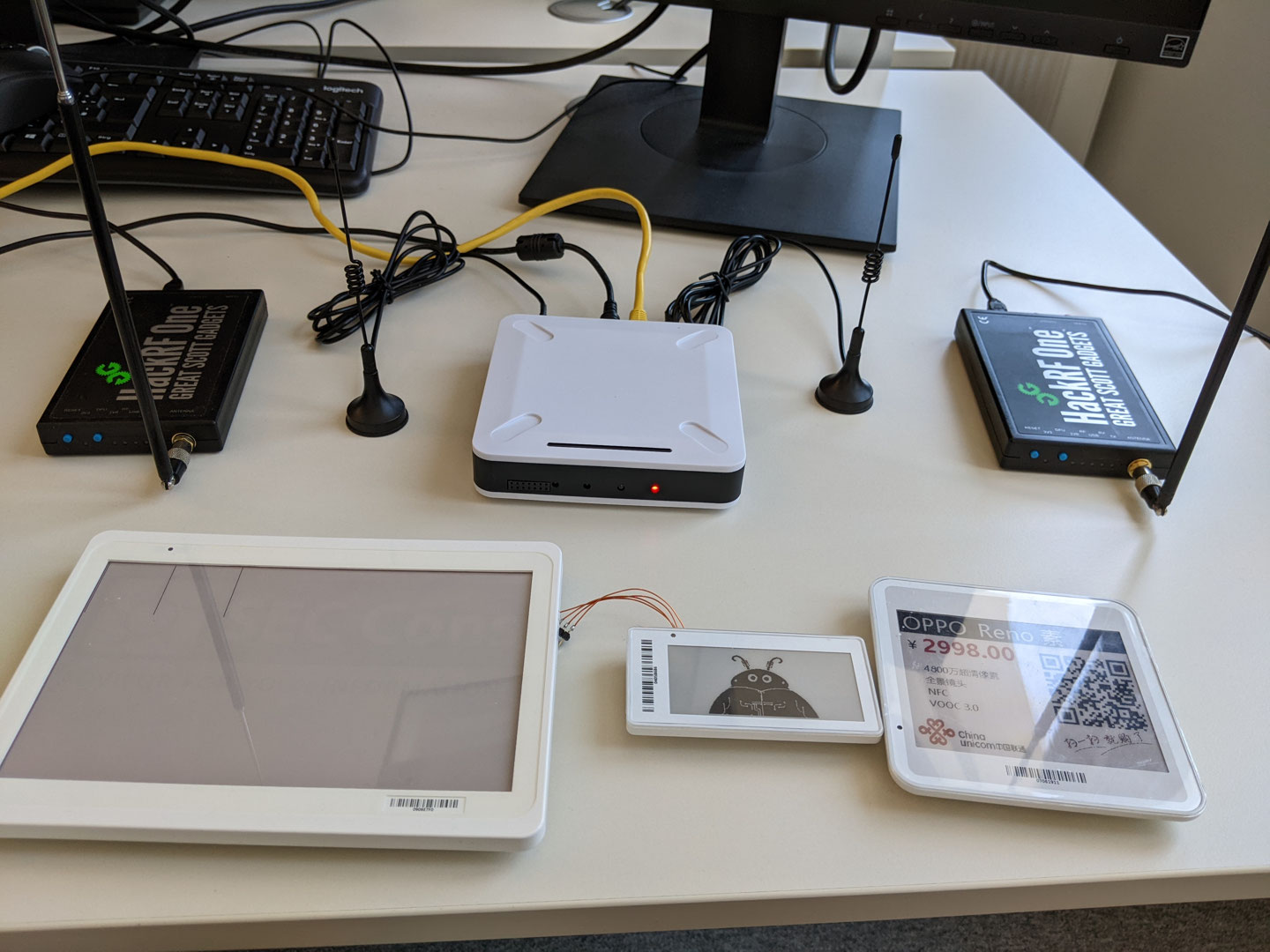
We took apart multiple ESL tags distributed by a chinese manufacturer. These tags are especially popular in China and consist of an e-ink display and an LED. The base station will be connected to the local LAN and will translate packets to a proprietary 433MHz GFSK modulated protocol. We reversed this protocol and found multiple security vulnerabilities. The protocol does not protect against replay attacks. Hence, the tags can always be reset to an older price by replaying the previously recorded frames. Furthermore, we are able to craft our own packets and correctly modulate them with a HackRF. Therefore, we can fully control the display of all tags in a store. The only information required is the tag ID which is printed on the top of the label or could be sniffed from previous tag transmissions.
A GNURadio Sketch was developed to correctly receive all packets and to forward them to a UDP port. A Python program is listening on this port and analyzing all contents. In addition, the script can be used to easily reprogram any ESL tag.
On top of that, a quick hardware security assessment was performed. We decapped the MCU of an E-Tag, which was only branded with the line "E-Tag M1". It turned out to be produced by STMicroelectronics and is most likely an STM8 microcontroller.
All in all, this talk will lead through the teardown of an unknown RF device and showcase, how signals can be intercepted and analyzed with predefined GNURadio blocks and some custom Python code.
Steffen Robertz is a Security Consultant at SEC Consult who specializes in embedded systems. In his Job, he focuses on retrieving and reverse engineering of firmwares in order to find vulnerabilities. Due to his background as an electrical engineering student, he also takes interest in RF systems and hardware development. He already published multiple security advisories via the SEC Consult Vulnerability lab.